Introduction
Start by explaining that attackers don’t always need to “break in”—sometimes they just “ask.”
“In Active Directory, certain accounts are configured in a way that allows any authenticated user to request a password hash without ever touching the target’s machine. This is ‘Roasting,’ and if your service account passwords are weak, your domain is already compromised.”
1. AS-REP Roasting: The “Forgotten” Setting
The Vulnerability: Some accounts have the attribute DONT_REQ_PREAUTH enabled. This means the Domain Controller doesn’t check if the user is who they say they are before sending back data that contains a piece of the password hash.
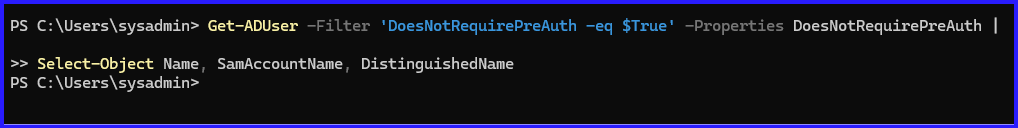
How to Audit (PowerShell): Give your readers this snippet to find the “at-risk” accounts:
# Find users with Kerberos Pre-Authentication Disabled
Get-ADUser -Filter 'DoesNotRequirePreAuth -eq $True' -Properties DoesNotRequirePreAuth |
Select-Object Name, SamAccountName, DistinguishedName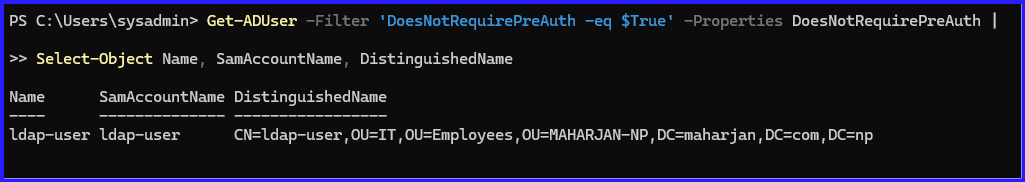
The Remediation:
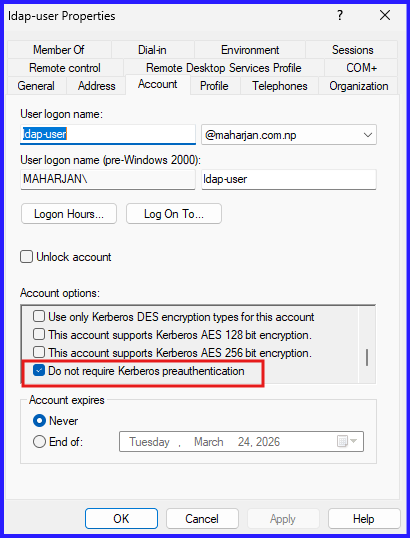
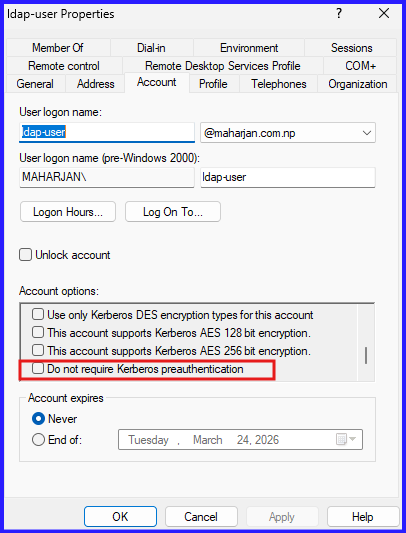
- Step 1: Identify if the account actually needs this (usually only very old legacy apps).
- Step 2: Uncheck “Do not require Kerberos preauthentication” in the Account tab of the user properties.
- Step 3: If it must stay on, ensure the password is 30+ characters.
2. Kerberoasting: The Service Account Trap
The Vulnerability: Any user in the domain can request a service ticket (TGS) for any account that has a Service Principal Name (SPN). The ticket returned is encrypted with the service account’s password hash. Attackers take this ticket home and crack it using a GPU.
How to Audit (PowerShell): Help your readers find all accounts that could be “Kerberoasted”:
# List all user accounts with SPNs (Potential Kerberoasting targets)
Get-ADUser -Filter {ServicePrincipalName -ne "$null"} -Properties ServicePrincipalName |
Select-Object Name, ServicePrincipalName, UserPrincipalName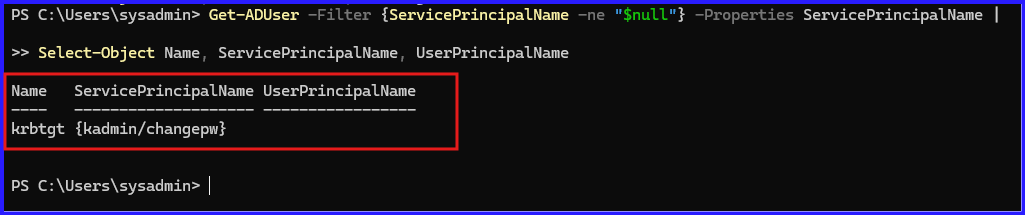
Summary of Key Concepts
- AS-REP Roasting: Targets accounts where “Kerberos pre-authentication” is disabled. Because the Domain Controller doesn’t require the user to prove their identity first, an attacker can request an authentication ticket and receive an encrypted blob that can be cracked offline to reveal the plaintext password.
- Kerberoasting: Targets service accounts that have a Service Principal Name (SPN). Any authenticated user can request a service ticket for these accounts. Since these tickets are encrypted with the service account’s password hash, attackers can extract them and use brute-force tools (like Hashcat or John the Ripper) to crack them offline.
Audit & Remediation Steps
To secure your environment against these vulnerabilities, follow these primary defensive measures:
- Enforce Pre-Authentication: Audit Active Directory for any user accounts with the
DONT_REQ_PREAUTHflag and enable Kerberos pre-authentication immediately. - Use Group Managed Service Accounts (gMSAs): Transition traditional service accounts to gMSAs. These have 120-character, complex passwords that are automatically rotated by Windows, making offline cracking practically impossible.
- Strengthen Password Policies: For service accounts that cannot be gMSAs, ensure they use long (25+ characters), complex passwords. Kerberos roasting’s effectiveness relies entirely on the weakness of the underlying password.
- Enforce AES Encryption: Disable legacy RC4 encryption and ensure accounts are configured to use AES-128 or AES-256, which are significantly more resistant to modern cracking techniques.
- Monitor Event Logs: Watch for specific indicators of compromise (IoCs) such as:
- Event ID 4768: TGT request (look for Ticket Encryption Type
0x17for RC4 or accounts with pre-auth disabled). - Event ID 4769: Service ticket requests (monitor for an unusual volume of requests from a single user).
- Event ID 4768: TGT request (look for Ticket Encryption Type
Conclusion
Securing Active Directory against roasting attacks is not about a single “fix” but rather about maintaining strict credential hygiene. By eliminating misconfigurations like disabled pre-authentication and replacing weak service account passwords with managed identities (gMSAs), you can effectively close one of the most common pathways used by adversaries to gain a foothold in the domain. Given your focus on Exchange Server and Active Directory upgrades, ensuring these legacy vulnerabilities are remediated is a critical step in modernizing your infrastructure’s security posture.